Several factors are contributing to rising rates of BNPL fraud, Sift’s trust and safety architect Brittany Allen said. Through its end-to-end Digital Trust and Safety Platform, Sift helps clients proactively stop fraud at crucial transaction points while fuelling growth. Sift also works with clients to help them use their services best.
BNPL services are increasingly popular, Allen said. With rising prices, many consumers have less money, leaving more to turn to BNPL.
Contributors to rising BNPL fraud
Fraudsters are also gravitating to it. In November, the number of blocked BNPL transactions rose 109%.
One key reason is in a system’s design, Allen explained. The BNPL process allows criminals to use stolen credit cards with lower limits to buy higher-value items due to purchases being broken into installments.
“They can buy a $2,000 laptop, knowing they will never make the subsequent payments,” Allen said. “The merchant will lose that first payment due to fraud via a chargeback, or the BNPL provider will, depending on the setup.”
See also:
Another contributor to rising BNPL fraud rates is the availability of one-time password bots on the deep and dark web, Allen advised. Scammers, along with social engineering, use them to convince legitimate account holders who receive an SMS message as part of the two-factor authentication process to hand that over to them. They’re organized, using automated scripts, pleasant voices, and citing the specific companies mentioned in the SMS.
Just as it is with any business, fraudsters benefit from a scalable product. On the day of our interview, Allen searched and found many bots for different BNPL providers at $10 each.
How system design can encourage BNPL fraud
Allen said a BNPL provider’s authorization process might leave them vulnerable to fraud. If they offer a 30-day grace period for the first payment, they might not catch dead, expired, or stolen cards that more stringent processes could flag. They may get through if the correct number of digits can be entered.

As soon as BNPL was introduced at scale, critics warned that insufficient checks were included in the rush to offer the service, lest merchants lose business. One vulnerability is that consumers are tied back to one email address when they open multiple BNPL accounts with different providers. Compromise that, and you can access every retailer linked to that account.
“We’ve also seen fraudsters advertising access to email accounts where it’s guaranteed that the person who owns that email address also has multiple BNPL providers,” Allen said. “Once you’re in their email, you can execute some of these password resets or otherwise get access to the accounts.”
Do you Yahoo!? Maybe you shouldn’t
Yahoo! email accounts are distinctly vulnerable. If fraudsters detect that a two-factor authentication prompt is being shown a certain way, they abandon it. If Yahoo initiated it!, they continue and will sell multiple accounts linked to Yahoo! addresses.
“I pulled a fraud posting this morning focused on a particular BNPL provider,” Allen said. “They specifically call out that they will only provide repayment if they made a mistake, and it was an invalid Yahoo 2FA account. They’re already saying that these are accounts you can get around.”
The pandemic drove more people online, including digital many digital newbies. The most vulnerable remain the most common users, Allen said. Account takeovers are increasing across the board. Fraudsters customize their methods to reach different segments. Specific software targets older users on desktops, while strategies to reach younger groups include TikTok approaches. Younger consumers often use BNPL because of thinner credit histories, and scammers know this.
It might get worse
Allen is waiting to see data from this shopping season. Higher prices and strained budgets will likely drive more shoppers to delayed payment methods. That means more shoppers who could be compromised. With few companies having robust in-house solutions, they must partner with companies that have those solutions.
One finding is likely, Allen said. She sees BNPL fraud costs being passed more frequently to merchants via higher fees to specific segments or across the board.
BNPL fraudsters have even learned how to use a company’s marketing materials against them, Allen said. If a company posts its partner retailers, they look for them on fraud forums and specifically target them.
“We find that fraudsters can specialize in certain merchants, and they know how to hit them to get purchases through successfully,” Allen said. “That’s another use of materials these providers have created for good to help legitimate consumers that are being increasingly spun as a marketing tactic on the deep and dark web.”
Botnets and poor connectivity
As BNPL services became more prominent, visionaries in the industry called for a universal system that could track individual BNPL use, much like a credit bureau. That would also combat another seam that sees fraudsters trick people into buying gift cards at one retailer that are redeemed at another. In many cases, the merchant cannot see the original purchaser if the different transactions are on separate networks.
Allen said those interested in seeing what fraud trends could next hit stateside should watch the goings on in the United Kingdom. That region is a hotbed for fraud innovation. Also, watch for automated push payments, which are hard to reverse.
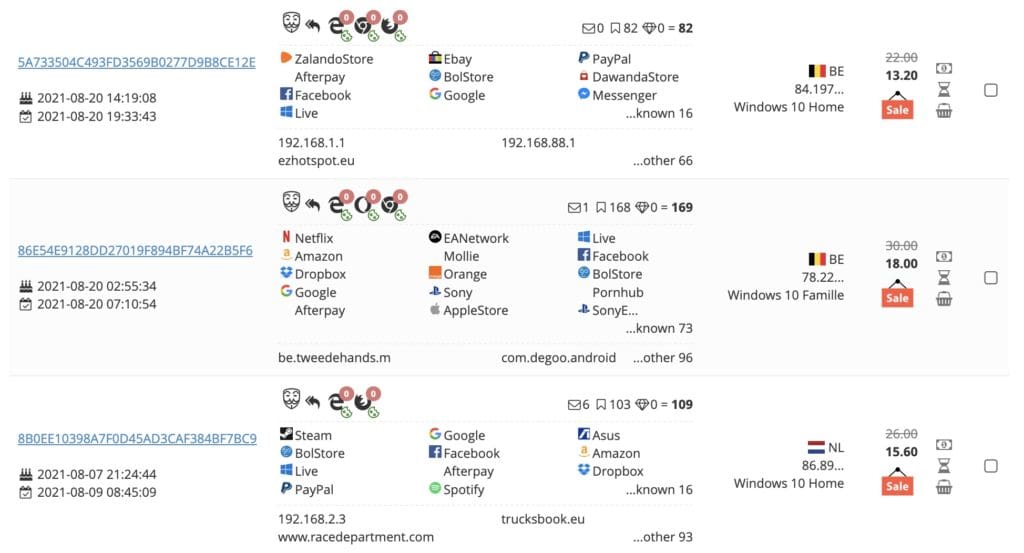
Fraudsters have also started to leverage botnets, Allen said. The Genesis Marketplace is online and on the dark web. It has 500,000 bots available for purchase.
“They offer those bots up to be purchased by anyone who joins the marketplace,” Allen said. “You get access to any login credentials that they have scraped from any browsers on that device. We’ll commonly see Chrome and Edge down to Opera and some mobile browsers.
“One compelling thing about that is that as long as that bot is active, and the person has not realized that their device is compromised, any changes they make on that device are also provided to the person who purchased access to the bot. So if I see strange activity within a buy now, pay later account, and I’m wondering how someone got in there, I change my password. If I do it on the same compromised device, the fraudster gets that immediately sent to them.”


